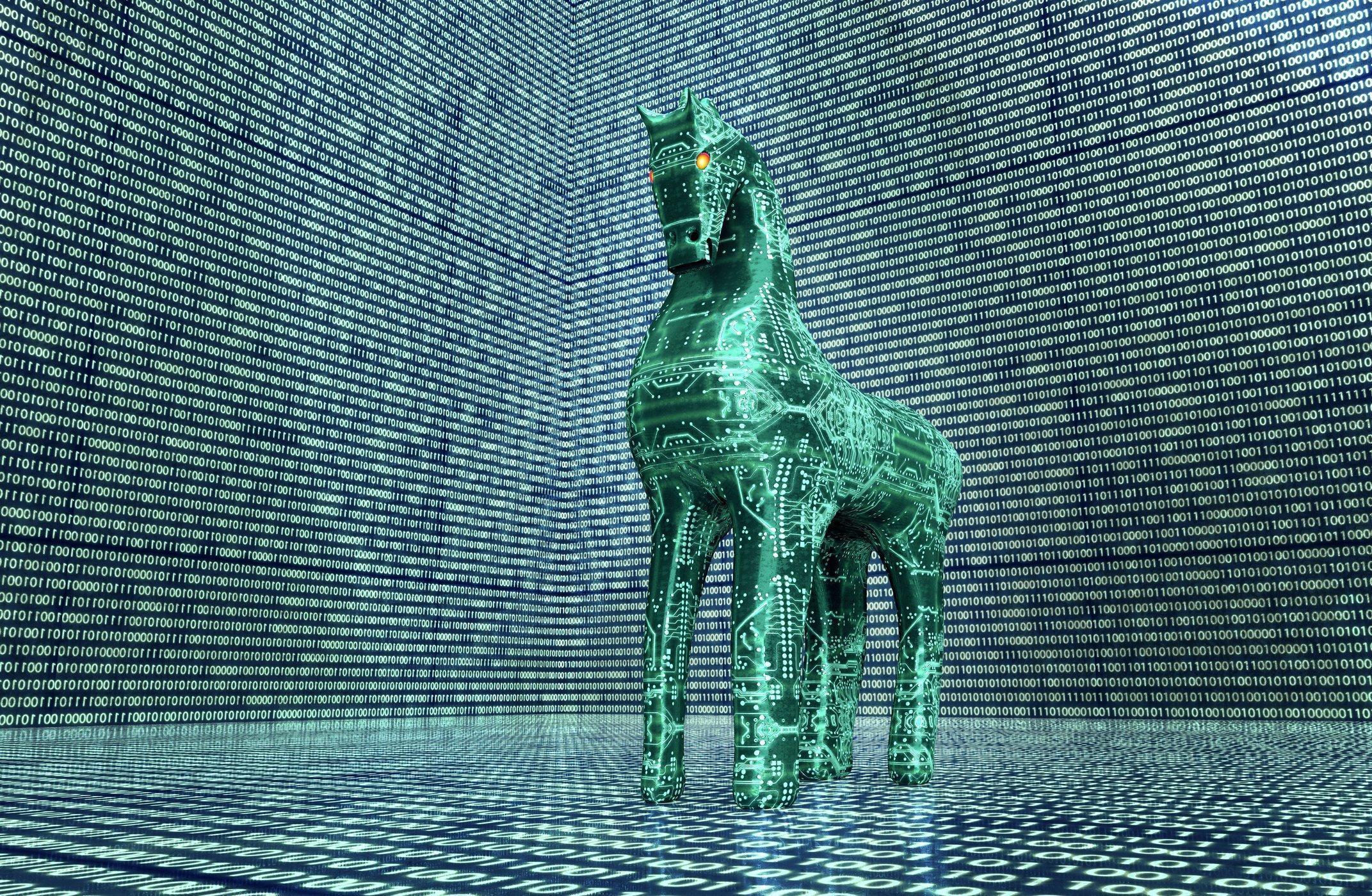
The GravityRAT trojan recently discovered by Cisco researchers has been lurking on computers for the last two years with a novel approach; it checks the temperature of the target computer to make sure it’s not being cataloged by anti-virus firms.
This innovation is just the latest way hackers have devised to get around malware detectors and cybersecurity experts implementing virtual machines under more controlled circumstances than can be reliably found in the wild–a practice known as sandboxing–to both identify and learn how to contain cyber threats.
Once identified, anti-virus and cybersecurity firms will update their software to protect against them–a process most consumers know about.
By being programmed specifically not to run on machines that are potentially studying them, the GravityRat virus has managed to avoid detection and become more sophisticated in its methods of attack.
Many virtual machines being run for anti-virus purposes run at higher temperatures than stand-alone computers or servers, an observation that provided hackers with a clever new approach to avoid detection.
After testing for the presence of a virtual machine, the virus itself deploys as a Microsoft Word macro, which duplicates itself and extracts a second program to the host computer that runs on a daily basis, thereby avoiding many of the telltale signs of an infection.
To read the original research article identifying the virus, click here.