Innovation can create new problems, and often even new industries. Two and half millennia after the invention of the wheel, we have traffic jams–made possible by the auto industry and Big Oil. That’s two industries right there. Fast food and high fructose corn syrup caused worldwide obesity, and gave rise to factory farming as well as the diet industry. (That’s two more!)
More recently, privacy has been a recurring issue when it comes to innovation, but it was a problem pre-Internet, as well.
Credit cards opened the door to overspending and account takeover as well as a host of privacy concerns around who gets to know your spending and bill-paying habits. Then there’s EZPass and FasTrak. Who doesn’t love automated toll roads? (Hint: People who don’t like being tracked.) The list is potentially endless, but no innovation has given rise to as many industries in the last fifty years than the Internet.
(Yep, the Internet is eligible to join the AARP this year!)
User privacy is an essential part of keeping your data and identity safe online; it’s something we talk about regularly on our podcast “What the Hack with Adam Levin.”
It’s no easy task to identify the 10 biggest Internet-related privacy failures masquerading as the next best thing since the World Wide Web, but here it goes.

1. Facebook
We all know Mark Zuckerberg started Facebook–now owned by Meta (how meta!)–in his college dorm room. And we all know the Zuck didn’t go to just any college. He went to Harvard. And of course his idea wasn’t just any idea, either. It became one of the most valuable companies ever.
While billions of us maintain accounts on Facebook, most people are aware that the company is no stranger to controversy. The meta-problem with Facebook stems from the product itself, originally built to help college students to get to know each other. A platform for self-expression and self-promotion of its users would be in a good position to sell all kinds of stuff to those users. It was just like TV, but a much more know-able, addicted and targetable environment.
“Getting to know” you is a process fraught with privacy issues. But Facebook took the position that “privacy” was synonymous with “marketing data.” That was the company’s value proposition.
The company’s insatiable appetite for data only grew. It got data about us from third parties like Spotify. Then it expanded by making itself the easiest way to access apps. The only catch: Facebook got all the information associated with the use of that app, and of course they sold access to it–bundled with all the other things they knew about you–to anyone looking to serve you a laser-guided ad.
The company is reputed to know when you’re going to experience a major life event long before you know it. Not exactly what those first college-age beta testers signed up for.

2. Google
In 1998, the world changed forever. Theatergoers were introduced to young Anakin Skywalker, a cute space kid destined to use the dark side of the Force to menace the universe and, in a similar vein, a useful little site called Google was launched.
Originally developed as an algorithm to share academic research, the company found a different, far more profitable groove: Search.
Google’s search engine was instantly legendary. It destroyed the competition, a rogue’s gallery of unknown companies to today’s digital natives: Try asking a Gen Y kid about Alta Vista, Metacrawler, Lycos, Yahoo Geocities, Excite or the host of other would-be portals to the Internet that people used in the late 90s. Google won because it was better. Search results were as close to real time as one could hope, and you could literally find anything.
With inordinate power comes massive responsibility–or at least that’s the hope. Google introduced a motto to help it navigate the moral murk of its mission to dominate the trafficking of information online: “Don’t be evil.”
Having dominated search, the company got busy adding new, powerful, and mostly free services including GMail, Google Maps, Google Photos and Google News. All of them harvested user information and used it to micro-target advertising but they also used our data to create new services. They knew what we wanted because of Google Search. Next came the Chrome browser, which gave Google even more information about us as it integrated everything from password management to payment information. Soon it was a near-impossibility to go online without coming into contact with Google.
When Google retired the “Don’t Be Evil” motto there was no ceremony because the company had become the Death Star-eating antichrist of consumer privacy.

3. Smartphones
When the first truly functional smartphones hit the market, it was exciting. Landlines were already headed for extinction, and it was really difficult to text on a flip phone. Having access to a pocket-sized computer with an easy interface that could take dictation as well as photographs and video all the while surfing the web and finding you great driving directions…who wouldn’t want that?
Smartphones prove a universal truth about awesome digital innovation: When it’s really good, there’s always a catch.
The features that made smartphones a must-have item collected user information–and they did it more effectively than Google and Facebook. Location tracking services and apps are the bread and butter of the digital marketing space. Loyalty store apps and banking apps reveal granular details about the things you buy. That handy camera has a default setting that snags hyper specific information every time you snap a picture, and your wireless provider keeps records detailing every phone call and text coming and going to and from your device.
Here’s the deal: Smartphones are the digital equivalent of a zoologist’s tracking tag. On our person each and every day allowing service providers and device manufacturers alike to compile enormous amounts of data on nearly every aspect of our lives. It really makes you wonder: Was it that hard to send a text on a flip phone?
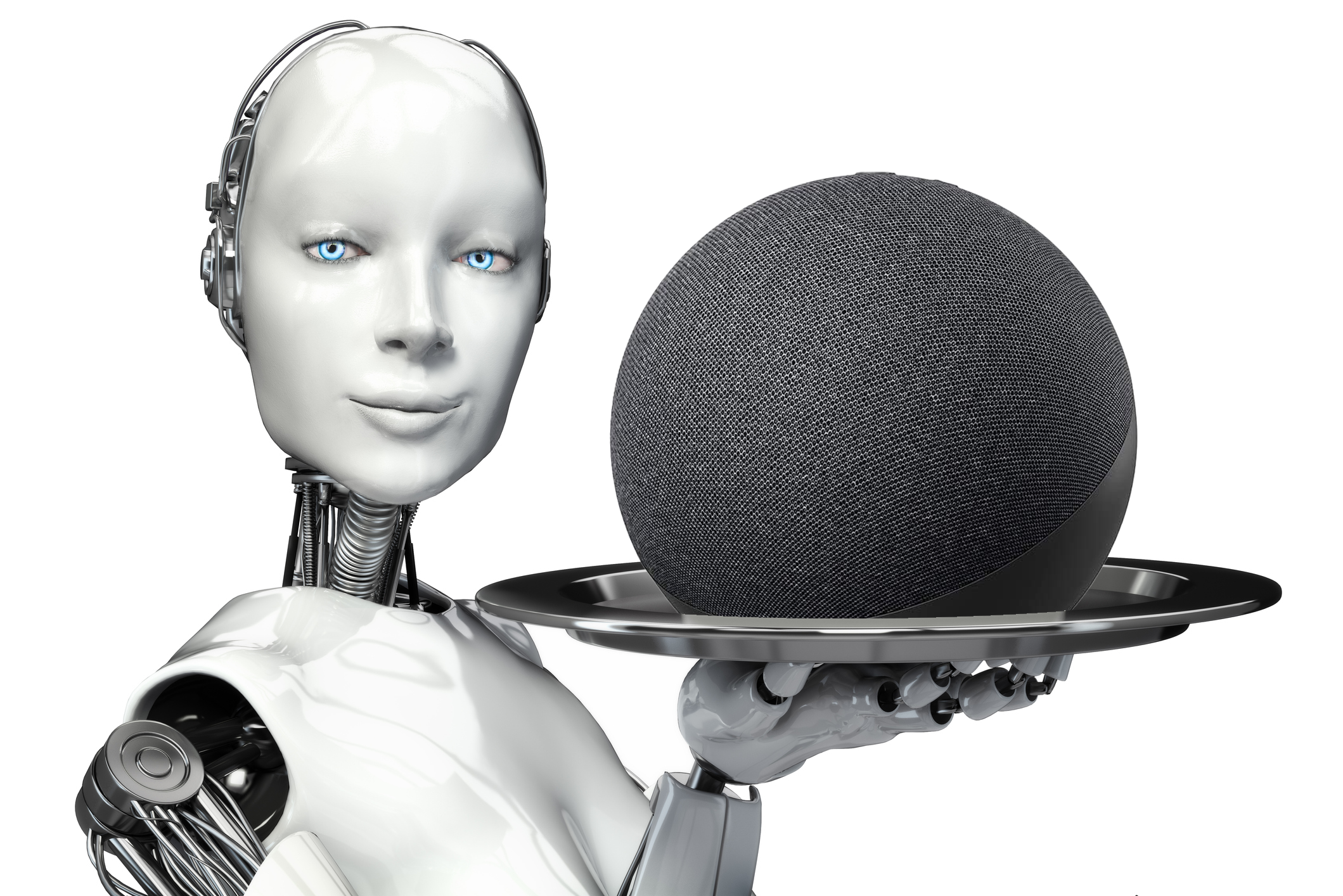
4. Voice-Activated Digital Home Assistants
Robot butlers are pretty common in utopian sci-fi, but only recently are they available to the average consumer and totally affordable. While voice activated home assistants can’t serve you breakfast in bed, they can get your breakfast delivered.
Being able to dim the lights, play music or choose a movie from the comfort of your recliner is pretty awesome, as is having an always-on device to call 911 when trouble is detected. There is absolutely nothing to complain about when it comes to these perks of owning a digital home assistant device.
The problem isn’t the machine, but what it’s connected to. Big data companies like Google, Facebook (Meta) and Amazon dominate the field. These companies and others have invested enormous amounts of time and money into developing a way to get a constant and detailed data feed about user behavior. Having an always-on microphone and camera in your living room is the ideal way to do that. It’s one of the reasons these devices are so affordable. They’re effective tools in the non-stop money grab known as the surveillance economy.
Until a company with strong privacy bona fides can offer a secure alternative to the voice-activated assistants currently on the market, it’s worth your while to get up from your chair and flip that light switch the old-fashioned way.

5. Smart IoT devices
A home filled with Internet of Things devices–any sort of connected appliance really–is a big deal these days, and very big business. There are tens of billions of IoT devices connected to the Internet and the number grows daily.
When it comes to IoT, if something is a part of daily life, the way it works has been digitized. Coffee makers, home heating and cooling systems, swimming pools, cars, lights, appliances of all stripe can now be controlled from an interface on your computer or smartphone. There’s nothing out there that hasn’t been connected (including bowling balls and chastity belts).
While this may conjure images of a cartoon character getting ejected from bed into a pressed suit, dumped down a chute into a chair, where freshly brewed coffee awaits, it would be more accurate to imagine your most intimate and sensitive private information displayed on a billboard.
We’ve all heard the stories about poorly protected IoT devices that come fully functional with default passwords like “Password,” “CoffeeTime” or that old tech crowd favorite “admin.” Perhaps you remember the health trackers that allowed anyone in a person’s network to see when they last made whoopie, or the sex toy that kept its data in a publicly accessible database?
The whizzbang offered by IoT can have a kaput effect on your reputation. It can also leak details about your life to third parties who exploit that data to sell you more stuff.
It’s not exactly true to say that IoT came with unintended privacy issues, since the privacy grab was built into many of the devices that allegedly improve life or make things easier. If you want a connected device, make sure the manufacturer is playing by rules you can live with, and has some semblance of privacy protection in place.

6. Remote Desktop Software
Anyone who has worked in IT or tried to walk a less-than-tech-savvy relative through a printer problem over the phone knows why remote desktop software rocks. Everyone who’s been tricked into providing a stranger access to their computer using that software knows there’s a downside.
Remote desktop software creates a digital tunnel for a third party (your tech-savvy relative, a hacker) to take control of your mouse and troubleshoot on your machine from somewhere else–anywhere else, which is exactly the problem with this software. Taking full control of another person’s computer is cool, especially if you are a scammer.
A number of scams exist that take advantage of this simple technological advance. It could be a phishing email or text, where a threat actor leads you to believe that there’s a problem on your machine and requests access to fix it when the only thing they do once they’re in your machine is steal credentials and otherwise compromise your digital life.
But that’s not the only issue. “Free” remote desktop products can collect information from devices, especially if the software is not un-installed once the remote work has been completed. Outdated or subpar remote desktop software that doesn’t use end-to-end encryption could allow information relayed from one computer to another to be intercepted by a hacker.
If you’ve downloaded remote-access software, uninstall it. While you don’t need it anymore, there’s a chance it needs you, or at least whoever put it there is enjoying free access to your computer.

7. Public Wifi
You may not believe this, but not so long ago there was no Internet. How did people communicate? Payphones, shouting, carrier pigeon, hand gestures, Morse code. When access to the internet became something consumers could buy into, it was slow and required a landline.
Wifi for the non-digital native was the closest any of us had ever gotten to an experience of magic in the world. Wifi takes an internet signal and broadcasts it through radio waves. As long as your device is within range of a wireless router and is able to connect to it, you can use the signal to go online. Public Wifi is awesome. Right?
Sorta. In much the same way that multiple people can listen to the same radio station, an unprotected Wifi connection means that, at least in theory, the information you’re sending and receiving can be tuned into (intercepted, accessed, exploited) as well. It’s technical, but all you need to know is that there are some really evil nerds out there, and they use public wifi in a way that flies in the face of the convenience it’s supposed to offer. Also: If you’re using XYZ Company’s free wifi without a VPN to encrypt your activity, they have access to and will probably sell that data.
Would you talk about your most private issues, or divulge your bank balance out loud at a dinner party? Probably not, but whenever you use public wifi without a VPN, you’re communicating with strangers at a party.

8. Online quizzes
What color is your aura? Which Disney princess are you? How well would you do if you were “playing” Squid Game? What kind of pastry would you be if you lived in Iceland?
Online quizzes seem like a fairly anodyne distraction. No doubt they can be fun so long as you don’t take the results too seriously. (After all, only some of us can be smarter than Einstein.) So what could possibly be wrong with a stupid online quiz?
Investing a few minutes of your time during a coffee break to confirm your suspicions about which house the Sorting Hat would choose for you in a Harry Potter novel shouldn’t cause any real compromise, but it does.
By providing a thousand little details about your likes, dislikes, inclinations, emotional states, background and intelligence level, you’re helping quiz sites assemble a more nuanced mosaic of who you are — the sort of information that data companies use to target ads. When you share the link to the quiz with a friend, you’re explicitly letting them know more details about your social circle. You may even be giving away answers to security questions on your accounts.
If you want to know what breed you would be if you were a dog, just go to your local animal rescue and ask them. But bring a leash, because they’ll try to get you to adopt it.
9. Health trackers![]()
We all know getting more exercise is important. Every additional step you take during the day can increase your lifespan and your happiness. A quick stretch during the workday not only helps keep the blood flowing, it can lead to greater productivity.
Good health doesn’t have to be hard. It just requires a lot of repetition and stick-to-it-iveness, and the best health tracking programs are great at that.
Wearable trackers and apps buzz and vibrate when it’s time to get a move on or sit up straight; they track your vital signs, keep tabs on your weight and provide an interface for logging your diet. It’s exactly what the doctor ordered for many of us, and doctors do indeed prescribe the use of these services to their patients.
Here’s the rub: That data is valuable to a wide range of data-driven industries. If you get in the habit of running a few miles a day, you’re probably an ideal target for an ad for running shoes. If you never seem to get up off the couch, a life insurance company would probably like to send some memes your way.
Data companies have done their utmost to get as many details about your lifestyle and habits as possible; providing them with a 24-7 running account of your biological processes gives them a sizable, and intimate, piece of the puzzle.
This reality might explain why Big Data buys information from menstrual cycle apps, Google just acquired FitBit, and you keep getting ads for Spanx.

10. Facial recognition
Passwords are a pain to keep straight. Getting codes sent to your phone each time you log into an account is tedious. ID cards get lost. Wouldn’t it be nice if we could just look into a camera and get authenticated? After all, most of us are going to have the same face for the foreseeable future.
Facial recognition professionals are glad you feel that way. The original promise made by this particular branch of biometric authentication was a quick and easy way to prove you were you, no cumbersome passcodes or thumbprint scanners.
Companies and government agencies quickly jumped on board: Microsoft’s Xbox consoles automatically logged users into an account once their face was identified by an on-board camera. Apple’s iOS devices use facial recognition as a default security feature. Immigraton officers around the world use the technology to speed their work.
What makes facial recognition so convenient is the same thing that makes it feel like an Orwellian nightmare: It doesn’t require you to do anything other than have a face — cameras and AI do the rest. Once your face is turned into a data set, any internet-connected camera can let a third party know when you walk through the door. Maybe that’s why Meta, just dropped its use of facial recognition on its flagship site, Facebook. (They’re expected to continue to use it within their Orwellian ecosystem of “metaverse” products.)
It’s not just about stopping Jason Bourne at the airport. That late-night beer and Twinkie run he made on his way to exposing black ops are now part of his purchase profile. There is nowhere to hide.









