FireEye is a global leader in cybersecurity. The company disclosed this week that a data breach had occurred, announcing that “a highly sophisticated threat actor” compromised their systems and stole tools the company used to simulate cyberattacks and data breaches.
Here’s what you need to know:
- The threat actors responsible have yet to be identified. While the identities of the attackers are currently under investigation, FireEye CEO Kevin Mandia indicated that the “discipline, operational security, and techniques lead [FireEye] to believe it was a state-sponsored attack.” Many security experts have speculated that the hackers responsible are linked to Russian intelligence servers, but nothing has been confirmed.
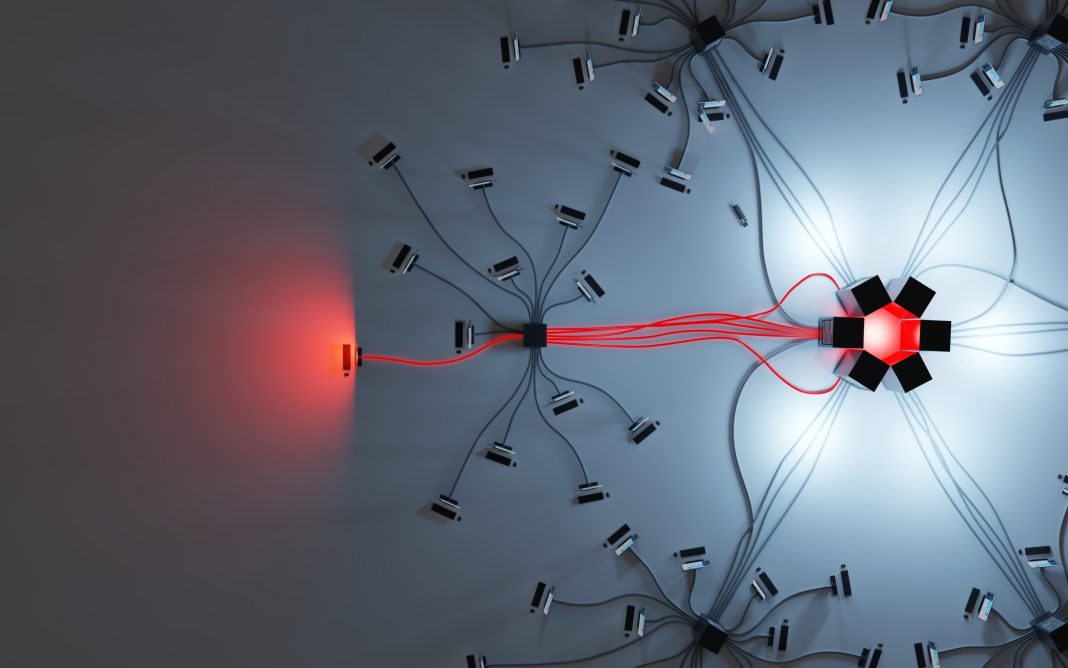
- The hacking toolkit used by FireEye’s “Red Team” was compromised. FireEye’s breach disclosed that the threat actors behind the attack had acquired “scripts, tools, scanners, and techniques” used by FireEye security experts to simulate data breaches and cyberattacks. Some of the tools described were modified versions of publicly available security testing tools, and others were developed in-house by FireEye and were proprietary.
On a practical level, this means the threat actors can add FireEye’s tools to their own arsenal of hacking techniques and methodologies. FireEye has indicated that it has not yet detected their methods or tools being used.
- None of the hacking tools exploited “zero day” vulnerabilities. The tools FireEye used to simulate and demonstrate hacking attacks exploited known vulnerabilities in systems. Software and IT administrators are urged to apply the most recent security patches to their systems to reduce potential risks.
- The breach reveals how FireEye simulates a cyberattack. Even if FireEye’s red team was exploiting known vulnerabilities, having access to their toolkit would undoubtedly be valuable to show threat actors how such vulnerabilities were being exploited and what strategies were being used.
- The stolen tools may also help threat actors operate more efficiently. Even if the scripts, tools, scanners, and techniques compromised were already released in one form or another online, having a more sophisticated version of an existing tool can help compromise a target more quickly, or make a cyberattack harder to detect.
FireEye was trying to keep these tools under lock and key for a reason, and the loss of control over them can and does represent a potential new danger to businesses, government agencies, organizations, and individuals worldwide.