Get in Touch
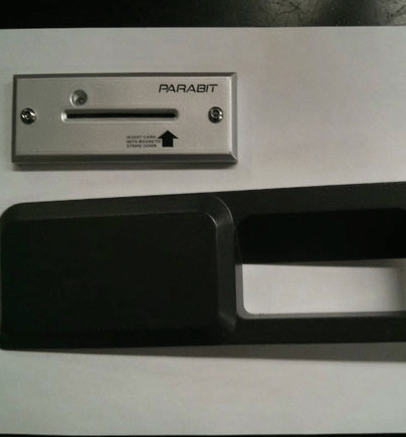
You probably know that criminals have long figured out how to trick people into handing over their credit card information. One way is the...
Watch an episode of SVU, Law & Order or CSI on TV, and you’re bound to hear about doctor-patient confidentiality in hushed, almost reverent...
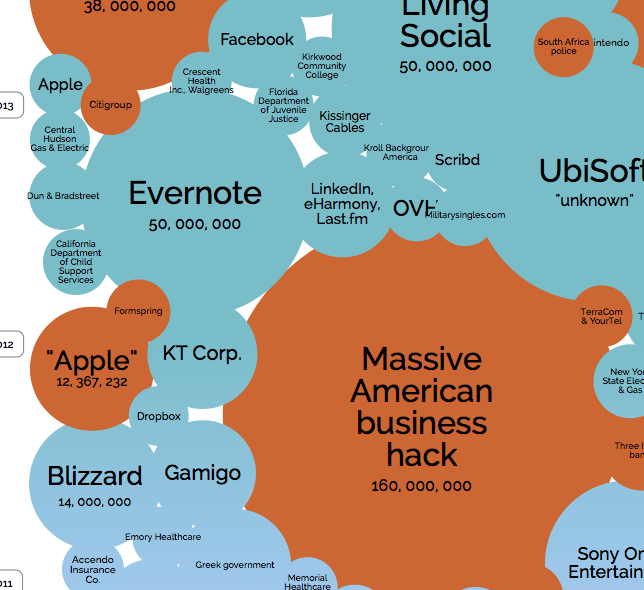
For those who think I've been beating the war drums about data breaches a lot, take a look at this chart brought to you...
There is an Apple enthusiast I know – and I'm sure you have a similar friend – who used to gleefully brag about all...
Yesterday a cybersecurity firm reported that 360 million newly stolen credentials were available for sale on the deep web. The breach reportedly includes one...
The storm of consumer-focused data breaches started off as intermittent downpours -- Choicepoint, TJ Maxx, SONY, LinkedIn, Twitter, Adobe Systems -- and is now...
I was on ABC News Radio yesterday right after news broke that the University of Maryland had suffered a major data breach involving information...
If some in the small business community thought to themselves, “better them than us,” after hearing that hackers had breached mega chains Target, Neiman...
Regular viewers of MTV’s series “Catfish” (in which online-only, deceptive relationships are pulled into the real world, albeit with cameras running) might think that...
To listen to some House Republicans at the Target hearing Wednesday, and the Senate Republicans on Tuesday, one would be forgiven for thinking that...